
What is a Buffer Overflow, Attack Types and Prevention Methods
5
(97)
Write Review
More
$ 15.50
In stock
Description
Attackers exploit buffer overflow issues to change execution paths, triggering responses that can damage the applications and exposes private information.

Buffer Overflow – CS2 – Java
Applied Sciences, Free Full-Text

How buffer overflow attacks work

System SOM to MX SSL certificate is about to expire Config High Both SOM To MX

Buffer Overflow Attack - Cybersecurity Glossary

PDF] A Compiler-Hardware Technique for Protecting Against Buffer

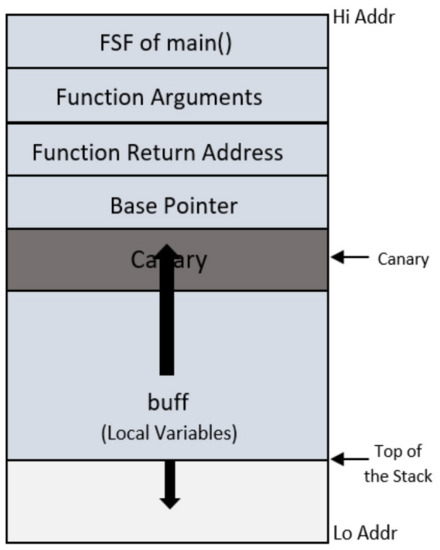
Exploit Development, Part 1: Anatomy of Buffer Overflows
Solved 1. Explain Exception Handling in C#. 1.1 What is, exceptions c#
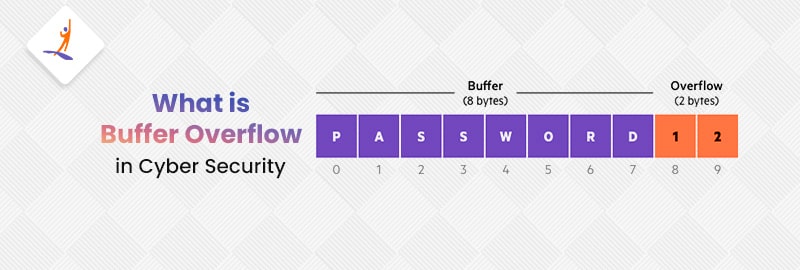
Buffer Overflow in Cyber Security - What is, Types, & Consequences

What is a Buffer Overflow Attack? ⚔️ Types, Examples
You may also like









